DoS/DDoS attack report against Deflect protected websites between Oct 7 to Oct 22, 2023
INTRODUCTION
Violence that engulfed Israel and Gaza in recent weeks has permeated the digital commons as well. From horrifying footage of murder on our computer screens to hateful discourse throughout social media platforms. The Deflect infrastructure has for many years been a secure home for Israeli and Palestinian human rights groups, media and civic institutions. Deflect staff continue to apply our project’s principles and terms of service to ensure that the network is not used as a platform for promoting violence or hate. We also seek our clients’ explicit permission before publicizing their association with Deflect and reporting on attacks that aims to silence them.
Since Oct 7, 2023, Deflect recorded six significant DoS/DDoS attacks against Israeli human rights organizations (btselem.org) that culminated with 54 million attack events hitting our edge servers. We also recorded 11 significant DoS/DDoS attacks against the Palestinian news website (palestinechronicle.com), with a total of 7 million malicious hits in various attack formation.
COVERAGE
- This report covers only L7 HTTP/HTTPS logs. There may be more attack traffic below L7, but is not covered in this report. Therefore we don’t provide traffic size information (such as 1GB of traffic per second).
- Attack with a higher “Ban rate” might underestimate the original scale of the attack. As after the Deflect ban, attacking IP will be banned on the firewall level and preventing any further request from that IP to hit our server.
- Sites with different tech parameters may result in different logging behavior. Site with JS challenger constantly enabled, challenging every request but do not firewall ban IP that failed too many challenges, may result in more attack traffic logged.
METHODOLOGY
To identify attacks from normal traffic, we employ the following methodology:
- Identify if a spike of total traffic / ban log existed over a 24 hour window.
- Narrow down to that time range for anomaly, which often includes:
- Excessive request hitting certain URL (such as root /)
- Excessive request with identical User-Agent from different IPs
- Evenly distributed User-Agent / HTTP Method that is too perfect to be true
- Excessive unique query string (such as ?v={rand}) to avoid cache
- Confirm if top traffic IPs triggered any of our rate limiting rules.
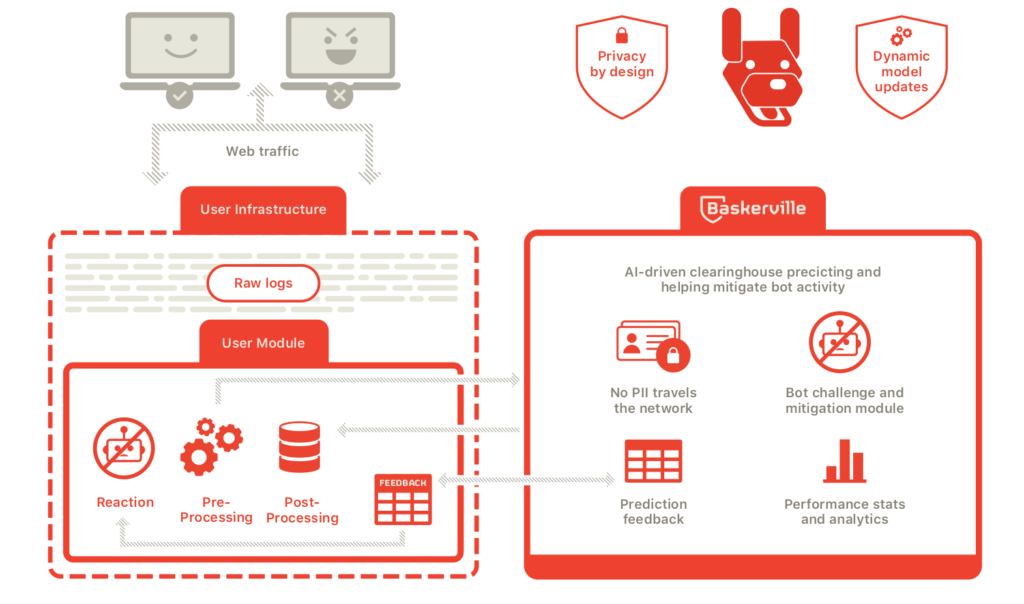
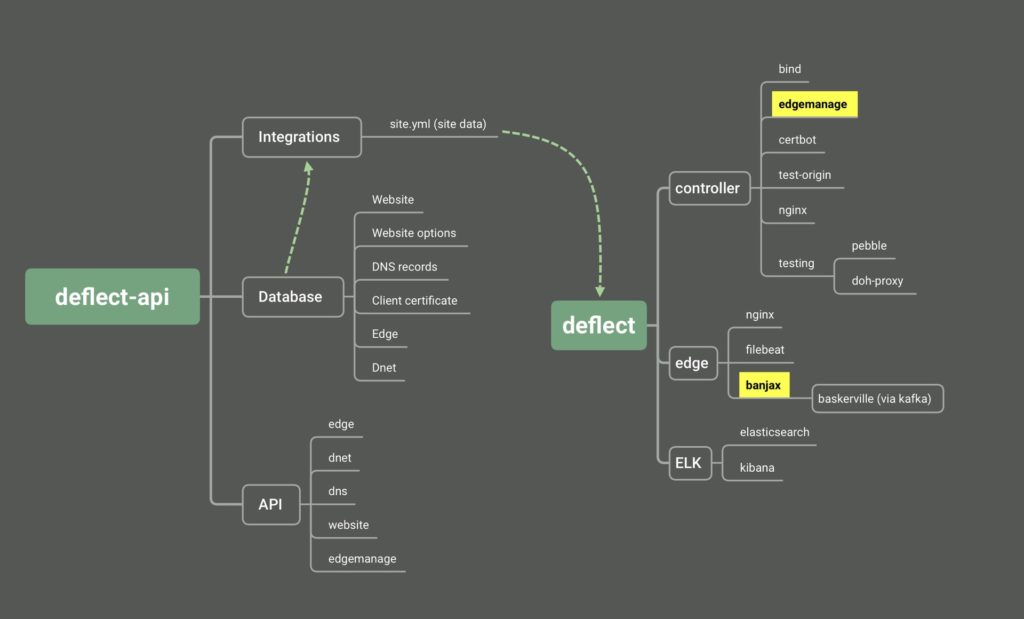
- Cross check with Baskerville system, a machine learning system that detects anomalous traffic.
ATTACK: BTSELEM.ORG
Parameters: JS Challenger: On / Fail challenger or hitting rate limit result: No ban
| # | Date | Start (+0) | Duration (s) | HTTP Req | RPS | Unique IP | Unique bans | Ban rate |
| B1 | 10/9/2023 | 20:37:51 | 997 | 52,497,380 | 52,644 | 245 | 165 | 67.35% |
| B2 | 10/13/2023 | 15:37:26 | 2665 | 291,192 | 109 | 1 | 1 | 100.00% |
| B3 | 10/16/2023 | 15:02:08 | 123 | 146,066 | 1,186 | 1,833 | 1,416 | 77.25% |
| B4 | 10/16/2023 | 22:32:55 | 483 | 1,068,436 | 2,211 | 3,611 | 2,403 | 66.55% |
| B5 | 10/18/2023 | 0:03:12 | 141 | 165,171 | 1,168 | 3,133 | 2,755 | 87.93% |
| B6 | 10/20/2023 | 13:24:30 | 181 | 133,930 | 739 | 2,606 | 2,281 | 87.53% |
Chart A: Deflect / Banjax ban log visualization of attack #B1
Attack #B1 stands as the most potent attack documented in this report. It achieved an average Request Per Second (RPS) of 52,644. The top 6 originating IPs dispatched an average of 3 million requests within a 10-minute duration. The assailants deployed a “Randomized Nocache Flood” strategy, using varying query strings to bypass caching. Notably, the same query string was observed being used by different IPs from various global locations.
Attack #B2 originated from a single IP: 46.210.30.130. However, an apparent misconfiguration in the attacker’s tool resulted in all their requests being rejected by our server.
Attack #B3 featured user-agent strings with minor variations in their version numbers, keeping a consistent foundational structure. Still, these weren’t entirely unique; the same user-agent string was detected being used by 37 different IPs.
Attack #B4 adopted a strategy akin to Attack #B3, but showcased a broader spectrum of user-agents and specifically targeted the /hebrew endpoint, as opposed to the website’s root directory (/).
Chart B: Baskerville Reaction to Attack #B4
Attack #B5 mirrored the tactics seen in Attack #B3 but employed a different set of user-agents.
Attack #B6 shared three identical User-agent string among the 2606 IPs.
ATTACK: PALESTINECHRONICLE.COM
Parameters: Js Challenger: Off / Hitting rate limit result: Firewall ban
| # | Date | Start (+0) | Duration (s) | HTTP Req | RPS | Unique IP | Unique bans | Ban rate |
| P1 | 10/8/2023 | 8:26:53 | 515 | 88,014 | 171 | 1,879 | 917 | 48.80% |
| P2 | 10/8/2023 | 14:42:26 | 925 | 86,991 | 94 | 1 | 1 | 100.00% |
| P3 | 10/9/2023 | 10:16:30 | 299 | 364,241 | 1,218 | 1,632 | 1,445 | 88.54% |
| P4 | 10/9/2023 | 22:34:09 | 154 | 1,198,752 | 7,764 | 1 | 1 | 100.00% |
| P5 | 10/10/2023 | 13:11:02 | 739 | 230,643 | 312 | 2,002 | 1,721 | 85.96% |
| P6 | 10/10/2023 | 17:06:39 | 668 | 2,869,176 | 4,294 | 708 | 532 | 75.14% |
| P7 | 10/12/2023 | 20:27:52 | 272 | 711,511 | 2,613 | 1,506 | 867 | 57.57% |
| P8 | 10/12/2023 | 20:57:58 | 248 | 738,380 | 2,977 | 1,142 | 938 | 82.14% |
| P9 | 10/13/2023 | 0:32:16 | 181 | 458,354 | 2,533 | 828 | 746 | 90.10% |
| P10 | 10/13/2023 | 9:25:37 | 177 | 291,291 | 1,648 | 759 | 710 | 93.54% |
| P11 | 10/21/2023 | 16:31:55 | 117 | 269,027 | 2,305 | 2,228 | 1,347 | 60.46% |
Chart C: Deflect / Banjax ban log visualization of attack #P6
Attack #P2 and #P4 was perpetrated by a single IP. Both targeted the HTTP port 80 and did not adhere to the 301 redirection to HTTPS. Excessive 301 requests were only subject to bans after October 14.
Attack #P6 was primarily executed by a single IP, which likewise did not adhere to the 301 redirects issued by Deflect.
Attacks #P7, #P8, #P9, and #P10 exhibited similarities in their approach; all employed a uniformly distributed user-agent string, implying that identical user-agent strings were observed across various IPs.
ATTACK CORRELATION
We observed significant overlaps in attack IPs across various DDoS attacks on palestinechronicle.com and btselem.org websites, suggesting coordinated attempts by the perpetrators. Here are the findings:
- Attack #P9 and #P10 shared approximately 50 common attack IPs.
- Attack #P7 and #P8 had about 30 identical attack IPs.
- Notably, attack #P7, #P8, #P9, and #P10 seems to originate from the same attacking source, evidenced by a strong overlap of source IPs.
- Attack #P3 and #P6 had six IPs in common. While attack #P1 and #P5 also shared six identical IPs. The recurrence of shared IPs in separate attacks suggests a possible, albeit weak, connection of a common attack source or affiliated entities.
- Attack #B4, #B5 and #B6 had 32 shared attack IPs, hinting that they might be from the same attacking source.
- There were also IPs that attacked both sites:
- IPs 186.121.235.66, 187.141.184.235, 201.91.82.155, and 36.91.45.11 targeted both #B3 and #P6.
- IPs 186.121.235.66, 187.141.184.235, 201.91.82.155, 36.91.45.11, 123.126.158.50, 223.112.53.2, 5.95.66.74, 79.107.146.14, and 190.90.8.74 attacked both #B3 and #P3.
- Of the 13 IPs that targeted attack #B1, three also attacked atack #P6 and six targeted #P3.
TOP ATTACKING IPs
This is a list of IP with excessive request logged on Deflect, associated with individual indecent (See # for matching attack ID).
| # | IP | AS | Requests Count |
| B1 | 198.50.121.146 | iWeb Technologies Inc. | 3,936,297 |
| B1 | 202.134.19.50 | CMC Telecom Infrastructure Company | 3,077,579 |
| B1 | 209.126.124.140 | HEG US Inc. | 2,908,415 |
| P6 | 104.199.133.2 | Google LLC | 2,802,394 |
| B1 | 185.191.236.162 | Rack Sphere Hosting S.A. | 2,751,354 |
| B1 | 200.30.138.54 | MILLICOM CABLE EL SALVADOR S.A. DE C.V. | 2,502,015 |
| B1 | 103.74.121.88 | The Corporation for Financing & Promoting Technology | 2,480,702 |
| P4 | 91.227.40.198 | Data Invest sp. z o.o. S.K.A | 1,198,752 |
| B1 | 113.125.82.11 | Cloud Computing Corporation | 848,330 |
| B1 | 37.211.21.205 | Ooredoo Q.S.C. | 831,118 |
| B1 | 173.212.197.82 | Contabo GmbH | 662,370 |
| B1 | 212.92.204.54 | A1 Hrvatska d.o.o. | 589,828 |
| B1 | 193.41.88.58 | Kyiv National Taras Shevchenko University | 542,676 |
| B1 | 109.70.189.70 | JSC Elektrosvyaz | 497,125 |
| B1 | 186.121.235.66 | AXS Bolivia S. A. | 417,661 |
| B1 | 93.180.220.67 | Intertelecom Ltd | 417,072 |
| B1 | 177.126.129.43 | Net Aki Internet Ltda | 399,074 |
| B2 | 46.210.30.130 | Cellcom Fixed Line Communication L.P. | 291,192 |
| P2 | 223.233.84.97 | Bharti Airtel Ltd., Telemedia Services | 86,991 |
| P7 | 23.247.35.2 | Global Frag Networks | 28,408 |
| P9 | 209.17.114.78 | Network Solutions, LLC | 25,476 |
| P10 | 209.17.114.78 | Network Solutions, LLC | 12,392 |
CONCLUSION
From October 7th to 22nd, 2023, both Israeli and Palestinian websites were subjected to coordinated and severe cyber-attacks, intended to overwhelm and take down these websites. These kinds of attacks, known as Distributed Denial of Service (DDoS) attacks, function like a traffic jam clogging up a highway, preventing regular users from accessing the website.
- Scale of Attacks: The Israeli human rights website faced attacks resulting in 54 million web requests, while the Palestinian news website experienced 7 million web requests. Think of these as millions of unwanted phone calls jamming up a hotline.
- Tactics and Techniques: The attackers adapted and used varied methods to bypass Deflect defences. Some tried to vary the attack requests in minute ways to fool manual rule-sets. Others used a more straightforward approach of sending a massive number of requests rapidly. In some instances, attackers tried to disguise their harmful requests by making them look like regular user visits.
- Shared Attack Patterns: We noticed that many of the attacks on both websites seemed to come from the same sources or groups. This is like recognizing the same group of troublemakers causing disruptions in multiple places. Specifically, the methods and even some of the internet addresses (IPs) used in the attacks were common across the two websites.
- Efficiency of Defenses: Our protective measures, think of them as security guards or filters, worked well in most cases. They were able to identify and block these harmful requests, preventing significant disruptions. However, attackers are persistent, and they keep trying various methods to bypass our defenses.
Over the recent period, our protective system, Deflect, has stood as a robust guardian for websites under its watch. Using sophisticated techniques, which include the power of machine learning, it has adeptly differentiated between regular and malicious traffic. This not only ensured that these cyber attackers were effectively thwarted but also maintained the uninterrupted service of the websites in question. It’s a testament to Deflect’s capability to handle intricate and aggressive cyber-attacks, safeguarding the essence and uninterrupted function of online platforms, and thereby supporting the freedom of expression online.