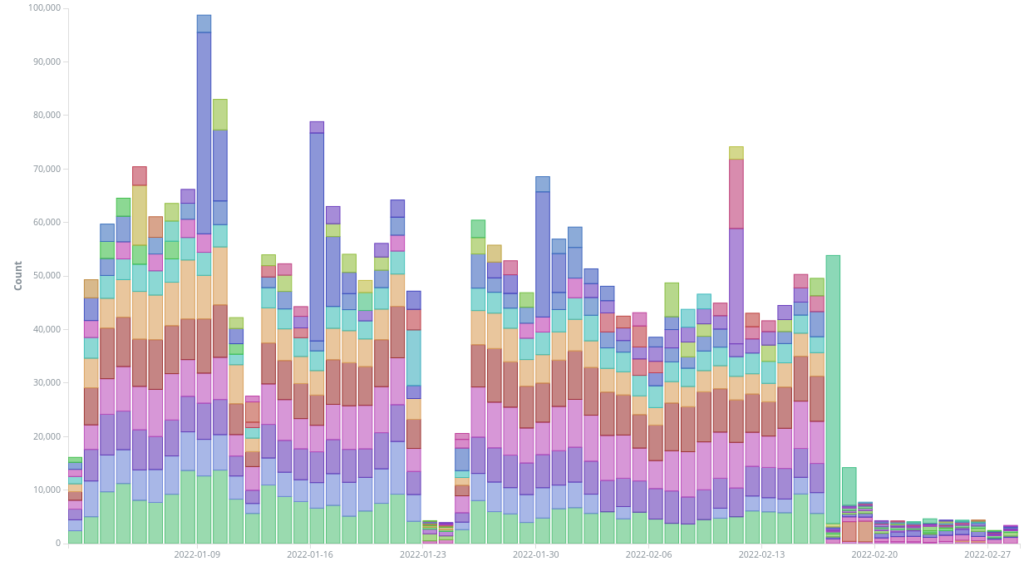
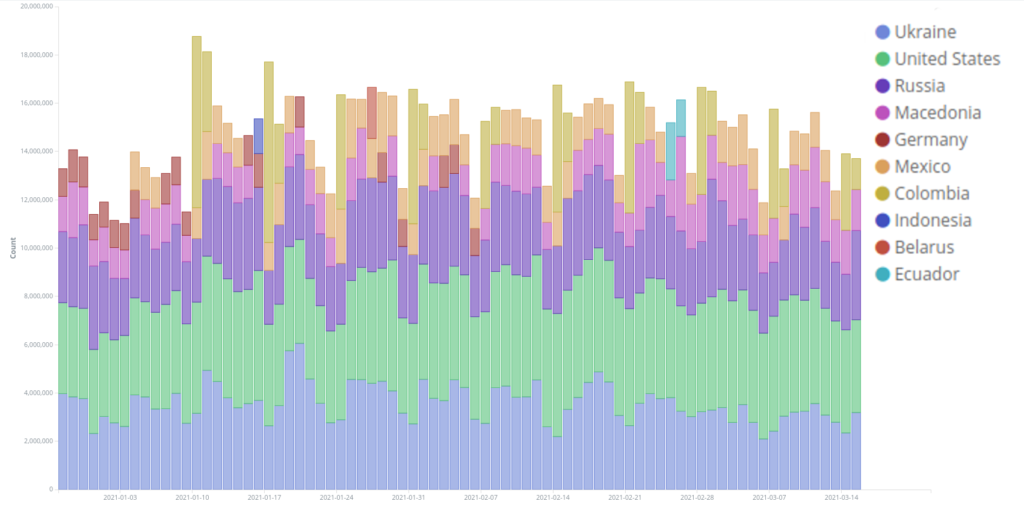
This was a busy month for Deflect’s mitigation tooling, with Banjax blocking almost 12 million malicious requests launched by 108,294 different bots. Due to the war in Ukraine, many people turned to Deflect protected Ukrainian media sites for information. Throughout the month Deflect served 1,128,751,920 requests (almost double than the previous month) of which 283,570,50 came from Ukraine – around 20% of our global traffic. 1,277,053 Ukrainians read Deflect protected websites – also a testament to the stability of the Internet there.
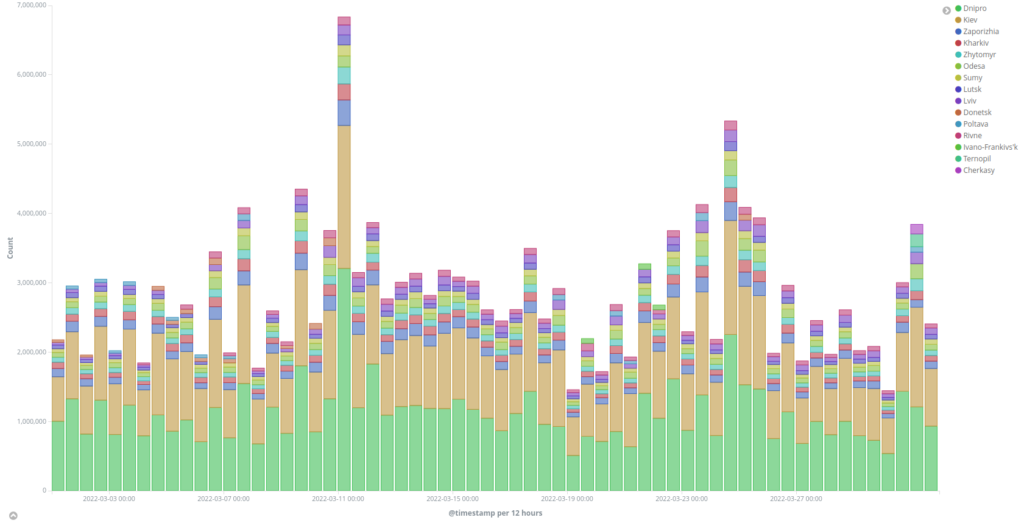
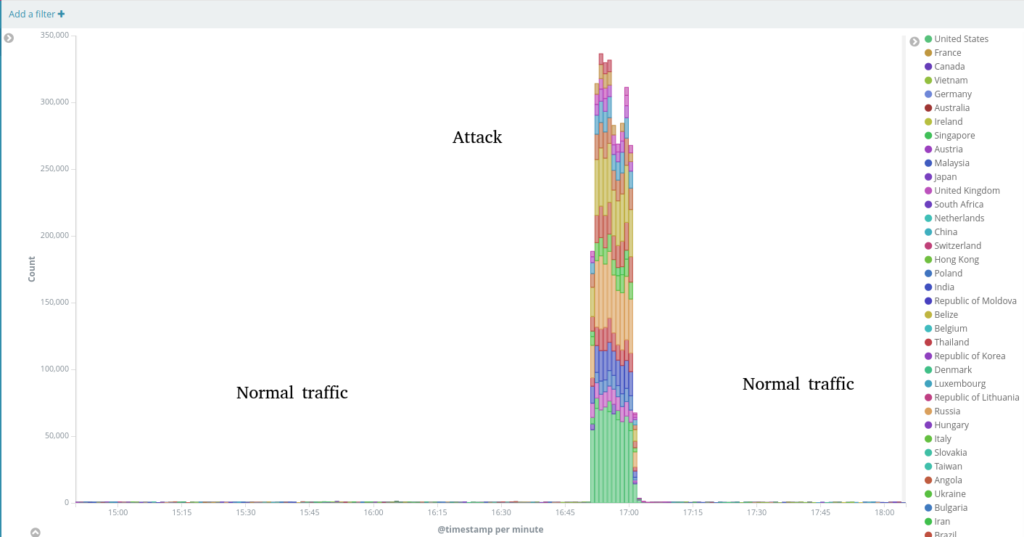
The biggest attack recorded this month was against informator.ua – a pan-Ukrainian news website with a focus on the Donbas region.
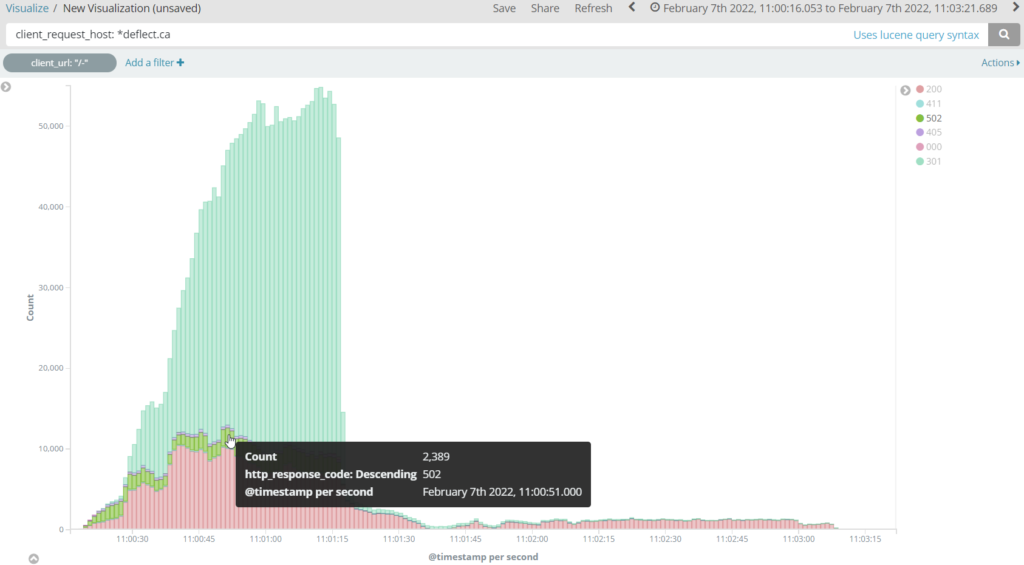
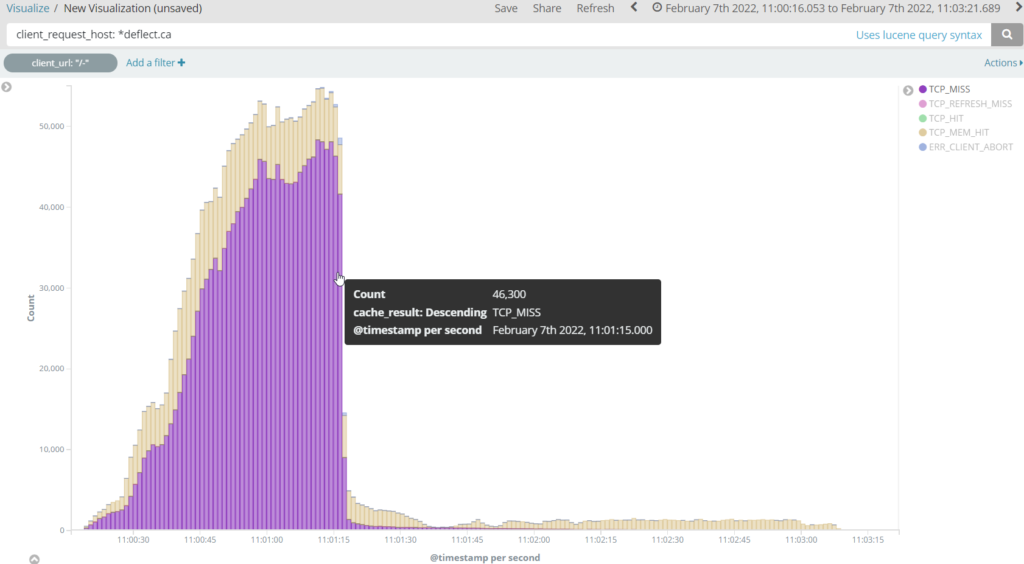
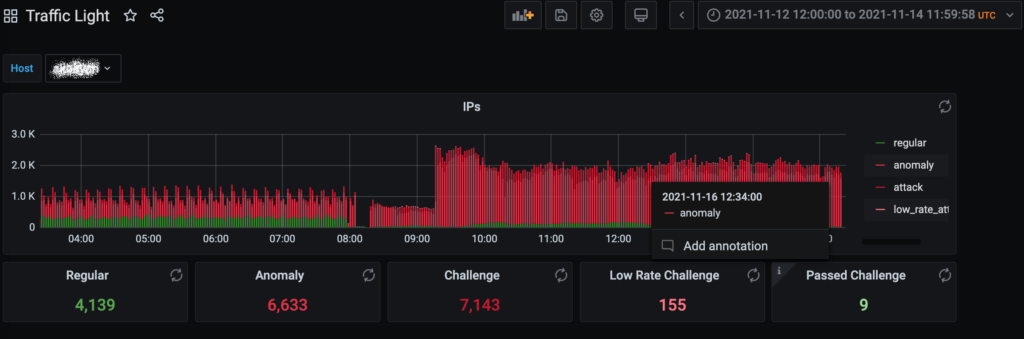
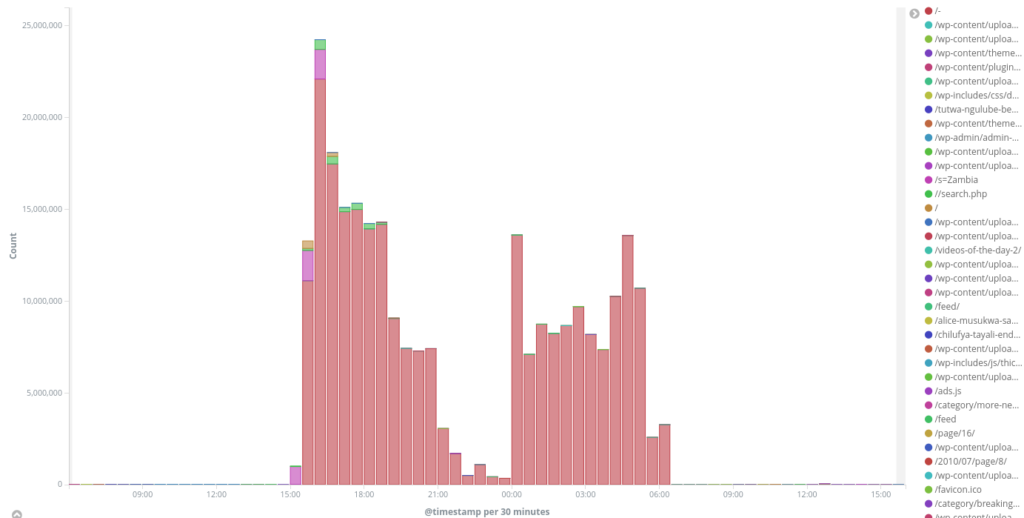
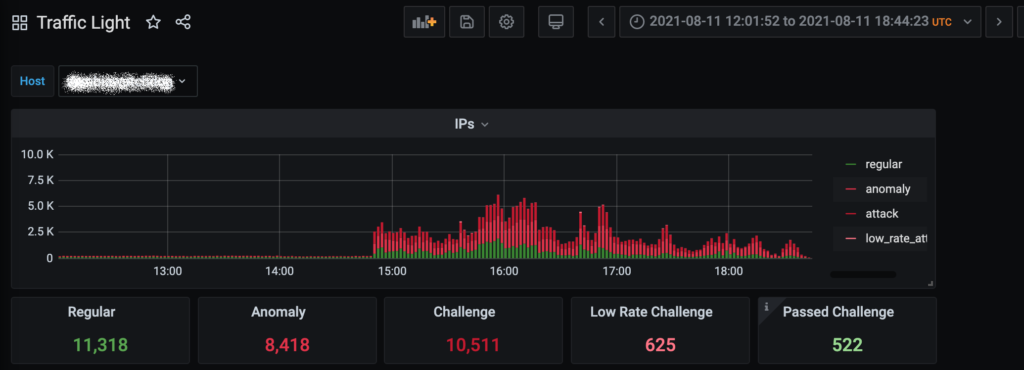
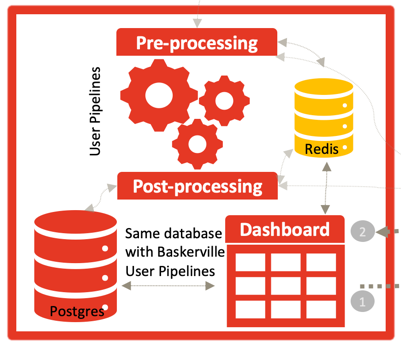
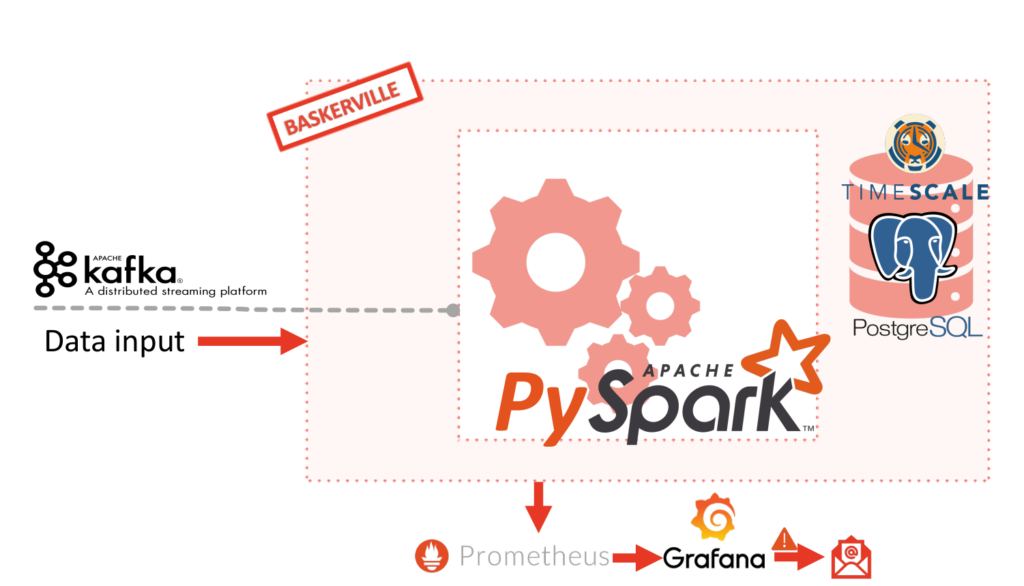
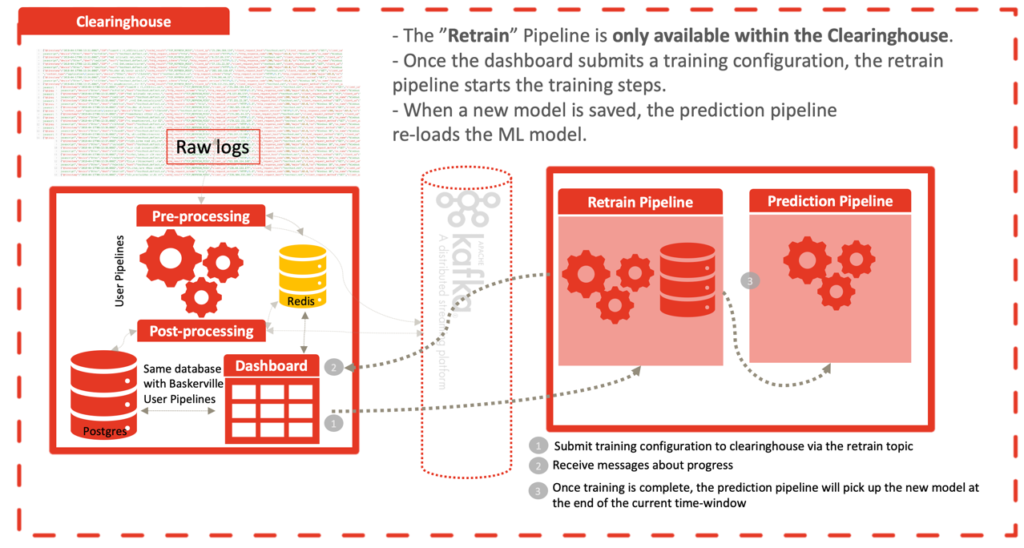
On the 31st of March, between 07:45-8:50 GMT+0 about 1,300 unique IPs were blocked by Deflect as they attacked informator.ua with GET /ru?8943563843054274 and POST /ru?829986440416200 requests, utilizing cache-busting techniques. These bots were from Brazil, USA, Indonesia, India, Bangladesh and many other countries, almost 1,000 of them seems to be infected MikroTik routers. Several hundred were compromised webservers and SOCKS proxies. There was a partial downtime for this website for about an hour as Deflect was not able to mitigate this attack fast enough to be sure no malicious requests are hitting the origin. The Baskerville system did not react as expected (this has been fixed). We enabled Challenger for this domain to be sure we can mitigate future attack without any issues for the origin. Our log aggregation and analysis system was affected by the overall amount of requests and was out of sync for a short period of time.
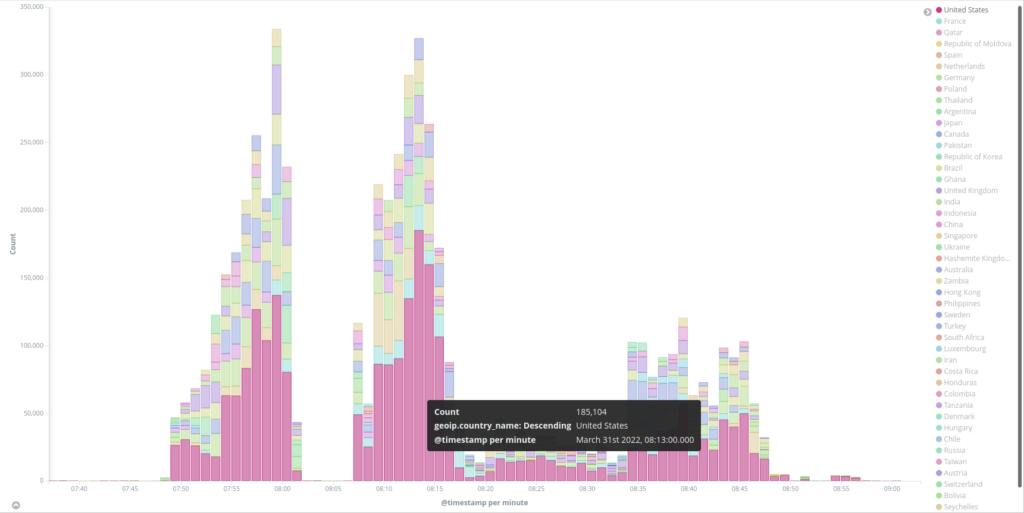
Top banned unique IPs by vendor
912 MikroTikRouter
232 Unknown
51 UbuntuServer
44 Torrouter
33 DebianServer
16 WindowsServer
6 WindowsSystem
6 RedHatServer
4 CentOSLinuxServer
Top banned unique IPs by service
875 MikroTik
232
49 Ubuntu-ssh
44 TorExitRouterHTTPheader
33 Debiansshheader
13 MikroTikSNMPinfo
10 MikroTikFTPserver
8 MikroTikPPTPserver
7 WindowsRDPServer
7 MSIISheader
6 WindowsNetBIOS
6 RedHatDNSheader
5 MikrotikRouterOSconfigurationpage
4 ApacheCentOS
2 WindowswithMSHTTPAPIWebServer
by client_url:
199940 /ru
102142 /ru/category/biznes/login
37312 /ru/ukraino-rossiyskie-peregovory-v-stambule-itogi
3 /ru/post-prev/45573